Align your business in compliance with the data protection and privacy regulations. Implement the best way to meet the specific requirements of this information age.
Oodles
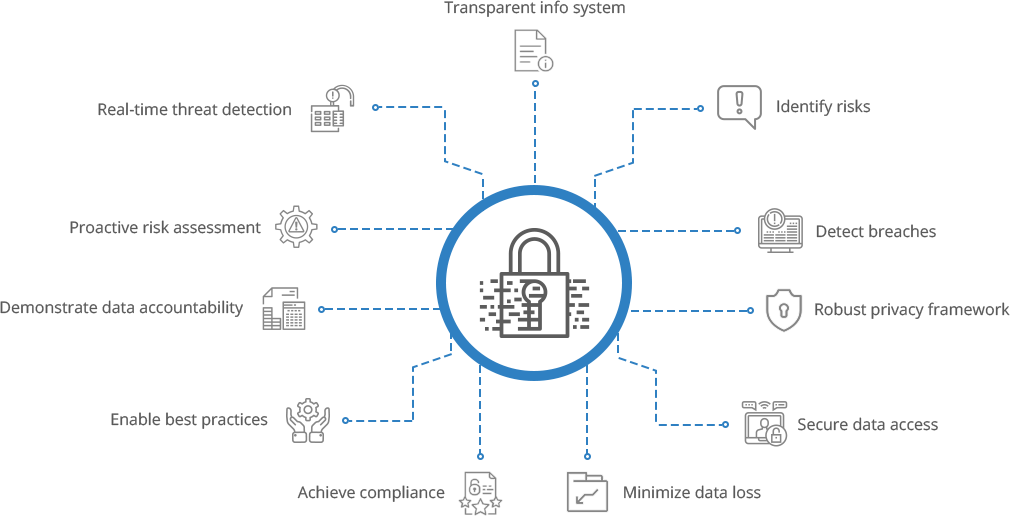
data protection and privacy services
assist you to maintain technical standards and guidelines to mitigate cyber risks. Our data protection services enable you to classify data and handle high-profile data breach issues by adhering to policies. Our data privacy services enable business compliance with applicable laws, rules, regulations, privacy, and security standards in a hassle-free manner. Ready to respond quickly and mitigate security and privacy risks? #bethenext.Safeguard your data environment
Map your data, eliminate gaps, adhere to standards and maintain organization’s reputation.
Protect privacy
Efficient operations
Earn customer trust
Minimize risks
Prevent breach
Business compliance
Cost-benefit relation
Support ethics
Data Privacy Services
We implement privacy maturity in your organization by preparing your business to meet the data privacy law and other global regulations’ requirements, reducing global sales friction, minimizing personal data storage and its process, protecting acquired customer data, measuring privacy-related business delay, reducing its impact through right actions, minimizing data breach while maximizing organization value.
Privacy Impact Assessment (PIA)
With our workshop based
PIA consulting services,
we help you identify the privacy risks, its impact on projects and operations, evaluate protection processes, and ensure conformance with applicable policy requirements.  Data Privacy Design Assessment
Data Privacy Design Assessment
With privacy by design concept, we ensure that privacy protection is embedded in the business processes, physical design, networked infrastructure, information technology, etc. We assist you to prevent privacy breaches, set default privacy, follow privacy embedded design, protect full life cycle with visibility and transparency.
- Data Flow Mapping
- Gap Assessment
Implementing the data flow map tool to gain visibility of licensed users, personal data flow throughout the organization and know why and what data is processed, held or transferred
Identifying and evaluating the gaps in the current practices against the implied privacy regulations or compliance

 Data Privacy Impact Assessment
Data Privacy Impact Assessment
Analyzing your organization's technical measures and determining how complex or detrimental the identified gaps can be
- Website Compliance Scanning
- Cookie Consent Management
- Universal Consent and Preference Management
Scanning website for tracking technologies such as cookies, privacy policies, and more
Tracking users’ behavior with their explicit consent on your site
Managing entire consent life cycle and maintaining consent audit trail to demonstrate accountability with regulations


Privacy Strategy and Implementation
Strategizing a cultural shift to bridge the gap, prioritizing the changes to be implemented, introducing new data process method and minimizing the data protection risks involved in the project
 Data Management
Data Management
Implementing data privacy strategies for accessing the data as relevant to business for actionable insights and decisions
 Data Analytics
Data Analytics
Predicting customer behavior and designing data compliant solution for actionable insights
Data Breach Notification and Incident Management
Power up your applications with robust data breach response plans mapped to latest global regulations, maintain records of notifications, automate workflows, respond and manage incidents easily and securely
 Streamlined Breach Investigation
Streamlined Breach Investigation
Identifying data authenticity, saving time with faster notification, pulling a report and scaling to generate massive and detailed reports, enabling easy tracking of the breach response process
 Minimized Failures
Minimized Failures
Preparing the organization for unexpected failures, reducing the severity, restoring the service operations by minimizing the impact of an incident, ensuring service quality, and availability


Third Party and Vendor Management
Implementing best practices for vendor management such as third party screening, due diligence program, auditing, pulling reports, follow ongoing monitoring procedures, review risk, and bring resilience
 Business Justification
Business Justification
Reducing data breach costs, costly operational failures, vendor bankruptcy, ethical obligation, and meeting regulatory mandates
 Four RMs (Risk-Measurement, Management, Monitoring and Response-Management)
Four RMs (Risk-Measurement, Management, Monitoring and Response-Management)
Analyzing and managing risks from vendors, customers, joint ventures, counter parties or the fourth parties by standardizing mechanism to deal, monitoring evolving risks, and responding to incidents
Data Protection Services
Along with guided consulting, we focus on developing a solid data protection strategy and its implementation plan that possess the controls, scalability, flexibility, and visibility to meet the needs of ever-changing threat and regulatory landscape. We assist you to prevent the cost of non-compliance with physical access mechanism and software solutions with data encryption, data masking, data monitoring, apt security measures, tracking patterns and identifying gaps.
Data Security Audit
We focus to have zero-trust concepts for your security assessment procedures. Our audit program involves data inventory completion procedure, data classification with reference to company policy, periodical review, align with laws and risk tolerance level of organization, data encryption, handling policies, protect data in transit and rest, manage security tools, assess compliance, leverage incident postmortems, and update policies.

Data Security Architecture
We align the security needs with the business needs by implementing the right security architecture and the technologies. It comprises of preventive, detective, corrective controls, directive controls, procedures and policies that protect your organization’s infrastructure and applications.

Data Security Implementation
We assist you to keep data security in check by implementing an effective data security strategy. We understand the data flow, categorize them depending on risk levels, probability of exposure, close the identified gaps, develop a sensitive plan, and implement it in your ecosystem successfully
 Data Encryption
Data Encryption
Adapting special and advanced encryption tools in all levels of Open System Interconnection (OSI) stack to protect against known, unknown, analyzed, or the futuristic threat scenario
 Threat Protection Implementation
Threat Protection Implementation
Implementing security measures that safeguard your organization against threats such as XSS attacks, SQL injection, CSRF, Null byte, DDoS, and more using leading-edge tools for investigation, and viewing real-time reports

GDPR Consulting Services
Our General Data Protection Regulation (GDPR) experts strengthen your privacy protection measures, achieve compliance and business benefits. We empower your organization with GDPR evaluation, roadmap development, meet privacy concerns of the market, and create customer trust.
 Gap Analysis
Gap Analysis PII Identification and Data Mapping
PII Identification and Data Mapping Incident Management Process Review
Incident Management Process Review Security Health Check and Maturity Assessment
Security Health Check and Maturity Assessment Third-party Assessment
Third-party Assessment Data Protection Impact Assessment (DPIA)
Data Protection Impact Assessment (DPIA) Security Architecture Consulting
Security Architecture Consulting Data Protection by Design
Data Protection by Design Policy Framework Review
Policy Framework Review Cookie Consent Management
Cookie Consent Management Data Protection and Privacy on Cloud
In the scope of GDPR and DPPA, we assist you to set an advanced cloud security architecture and ensure your data is secure on cloud. We help you to protect business and customers data as well and recommend the adept
cloud service providers
as required.- AWS Cloud Security
- Google Cloud Security
- Microsoft Azure
- IBM Cloud Security Service
Discover our related services
Services and solutions that work best with Data Privacy and Protection.
#DataPrivacyProtection Trends
Ready to innovate? Let's get in touch
Oodles Technologies | Data Protection & Privacy Services
Cookies are important to the proper functioning of a site. To improve your experience, we use cookies to remember log-in details and provide secure log-in, collect statistics to optimize site functionality, and deliver content tailored to your interests. Click Agree and Proceed to accept cookies and go directly to the site or click on View Cookie Settings to see detailed descriptions of the types of cookies and choose whether to accept certain cookies while on the site.









