Spring security basics
Posted By : Gaurav Kumar | 21-Jan-2021
Before we begin to deep dive into spring-security, we need to understand why we need application-level security. Since we have already OS-level security, server-level security then why we need this application-level security. The answer is pretty much self-explanatory, since we are developing APIs in Java, these endpoints are explicitly exposed to end-user that's why all the already applied security on OS-level and server are forcefully bypassed here.
So, Spring security is an application framework that provides:
- Login and logout functionality.
- Allow/block access to URLs to users.
- Allow/block access to URLs to logged in users and with certain roles(access control).
- Username/password-based authentication
- SSO/Okta/LDAP (Single sign-on authorization)
- App-level authorization
- Intra App authorization using OAuth
- Micro-Service security
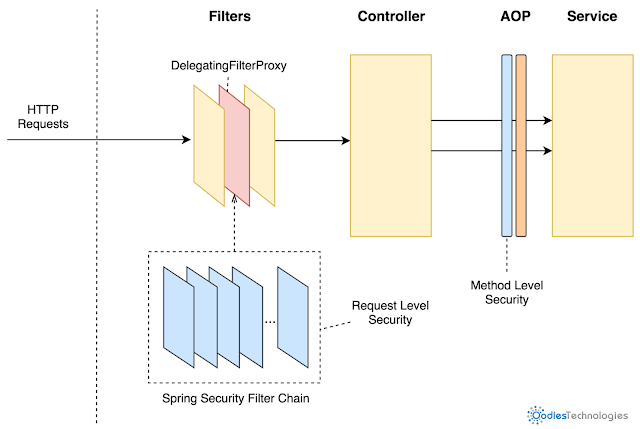
- Method level security
5 core concepts in spring-security
- Authentication: It is a way to uniquely identifies the requesting user by any one of the following methods:-
* Knowledge-based authentication by providing user name/password or pin or question ( like pet name etc.) that are actually provided by end-user at the time of registration.
* Possession base authentication is something like only you are at the possession of providing that information like OTP, access card, etc, that only you can have this.
* Multi-factor authentication is the combination of both the above knowledge base and possession-based authentication to make sign-in more secure.
- Authorization: It is a boolean check that confirms that is requested user is eligible to perform the requested operation or not.
- Principal: It is the environment or preferences a user has configured to his account, you can things principal as currently logged in user. where he has configured things according to his preferences, this may be different for a different user account.
- Granted Authority: It is a list of authorized activities to a particular user account. Like a user can view his balance, language preferences, transaction history. But he is not allowed to delete a particular transaction history.
- Role: It is the granted authority, or you can say it is a collection of granted authority based on the certain positions like admin has approx all granted authority present into the system but a user has not. So admin and users are two different roles here.
That's all required core concepts to dive into spring-security, in the next blog I will implement a sample spring boot service using spring security.
Hope you enjoyed this blog and find this useful.
Also Read: Sending HTML template based email in spring boot using a free marker
Why You Should Choose Oodles For SaaS Product Development?
We are a 360-degree software development company that provides cross-platform SaaS app development services to address varied software project requirements. We have an experienced team of Java, PHP, and Python developers who use advanced frameworks, tools, and SDKs to build scalable web and mobile applications with custom features. For more detail, reach us out at [email protected].
Cookies are important to the proper functioning of a site. To improve your experience, we use cookies to remember log-in details and provide secure log-in, collect statistics to optimize site functionality, and deliver content tailored to your interests. Click Agree and Proceed to accept cookies and go directly to the site or click on View Cookie Settings to see detailed descriptions of the types of cookies and choose whether to accept certain cookies while on the site.











About Author
Gaurav Kumar
He is always ready to grasp new tech and tools as per project requirement.